Background
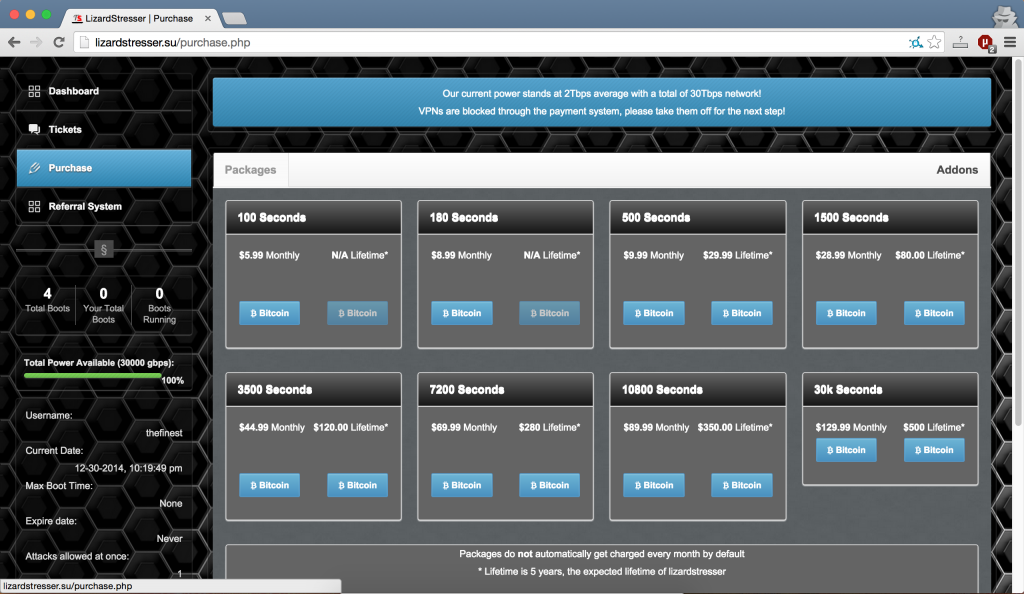
LizardSquad, the “hacker” group that recently DDoSed Microsoft’s and Playstation’s gaming networks, released a DDoS tool/service that can be found on www.lizardstresser.su.
LizardStresser is simply another booter, a tool that anyone (mostly script-kiddies) can pay to DDoS a target. Like every other booter, LizardStresser is accessible through a webpage (www.lizardstresser.su) where users can signup and pay for booter access.
Not surprisingly, LizardStresser is extremely poorly written, which led to me to find a user enumeration vulnerability in a few minutes.
Dumping Usernames and UIDs
Through lizardstresser.su’s ticket system, users can request customer support from admins.
After a ticket is created, a user can send messages through the ticket.
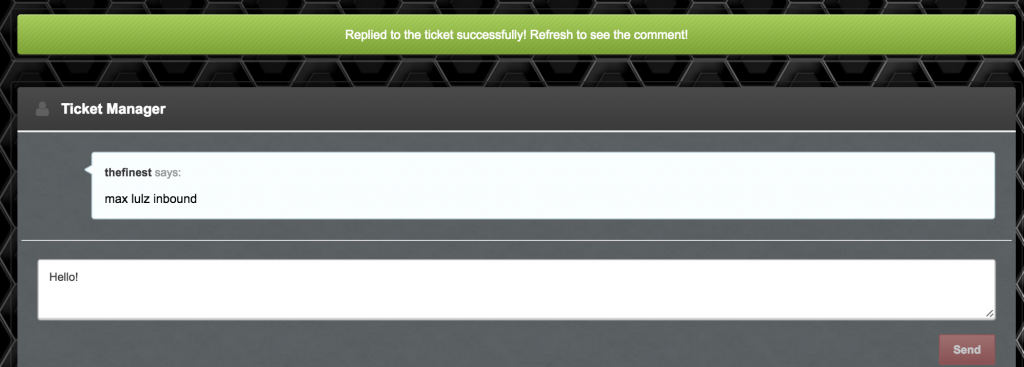
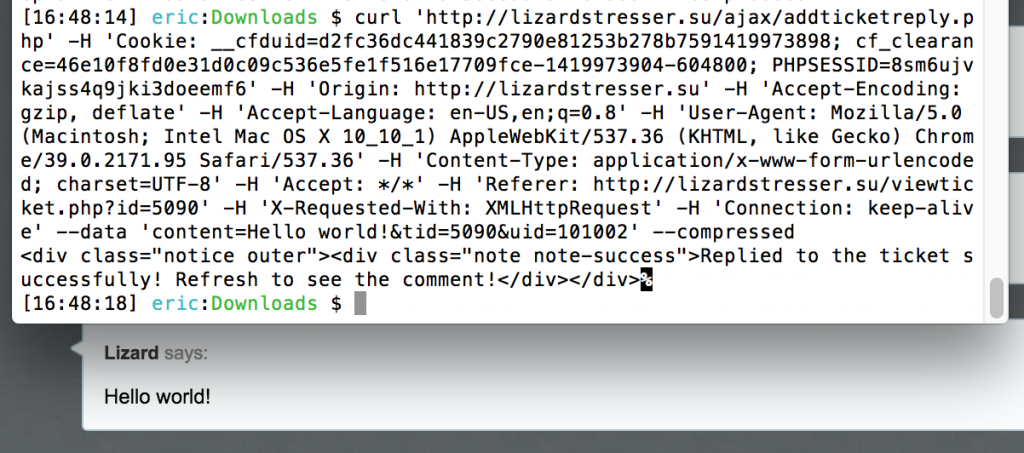
When the “Send” button is pressed, an XHR request is sent to “http://lizardstresser.su/ajax/addticketreply.php” with the parameters “content”, “tid”, and “uid”. The content refers to the message, tid is the ticket id, and uid is (you guessed it) the sender’s user id.
So what happens when we resend the request with a different UID?
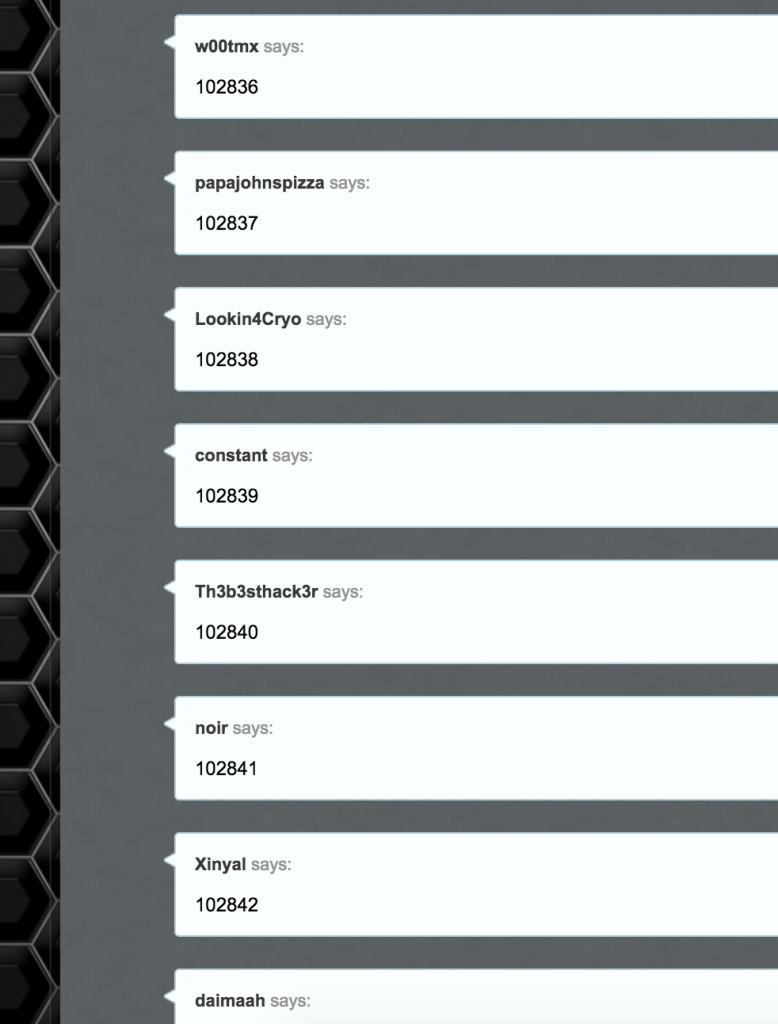
With an easy Python script, we can now fully enumerate all users:
And we get something like:
For a list of UID’s and usernames, visit the following link:
https://www.ericzhang.me/dl/?file=lizardstresser-user-dump.txt
Conclusions
Not surprisingly, I don’t recommend ever paying for LizardStresser (or any booter service). While user enumeration isn’t as interesting as a full database dump, I wouldn’t be surprised if anyone manages to find more vulnerabilities, especially since their platform is so poorly written.
Bonus Bugs
Bypassing Registration Limits
It seems that the front-end only lets you register one account per IP. This can easily be bypassed by manually setting an X-Forwarded-For header.
.htaccess Visible
LizardStresser.su’s htaccess file is publicly viewable. Doesn’t contain anything interesting though. Source
TitaniumStresser Clone
It seems that LizardStresser is a clone of TitaniumStressor. Aside from the same graphics, LizardStresser’s robots.txt contains: “sitemap: http://www.titaniumstresser.net/sitemap.xml”
I am profoundly grateful for the generosity and support you have extended to me. I am genuinely grateful for the spiritual support you offer. driving directions